This week’s roundup highlights state-sponsored cyber activity targeting government, critical infrastructure, and defense-related organizations, with a focus on strategic intent and geopolitical context.
Israeli Authorities Report Surge in Data Wiping Attacks
On 24 March 2026, Israeli authorities reported at least 50 data wiping attacks targeting organizations across the country, attributed to pro-Iranian and affiliated threat actors. The operations involved destructive malware built to erase systems and disrupt business continuity, with activity observed across several sectors during a period of heightened regional tension. Unlike traditional espionage-focused campaigns, these attacks appear intended to cause immediate operational impact and degrade confidence in organizational resilience.
Implications: This activity shows a continued willingness by Iranian actors to deploy disruptive cyber effects in support of Iran’s broader geopolitical objectives. While the current wave appears concentrated on regional targets, Iranian-linked actors have previously demonstrated intent and capability to target US and DIB-adjacent organizations, including incidents involving companies like Stryker. This suggests similar disruptive tactics may extend beyond the region in a future escalation scenario, especially as tensions between the US and Iran heat up.
Russian FSB-Linked Group Targets iOS Devices with DarkSword Exploit
On 27 March 2026, Proofpoint reported that the suspected Russian FSB-linked threat group TA446 (aka COLDRIVER, Callisto, SEABORGIUM) deployed a leaked exploit known as DarkSword to target Apple iOS devices. The campaign used a zero-click or low-interaction exploit chain to gain access to targeted devices, enabling surveillance of communications, data exfiltration, and persistent monitoring. The activity appears highly targeted, likely focused on individuals of intelligence value, including government personnel, diplomats, and other high-value targets.
Implications: The adoption of DarkSword by TA446 represents a critical expansion of the mobile threat landscape, where state-grade exploitation tools are now being commoditized and used by a broader array of actors following code leaks. For organizations in, or adjacent to, the US DIB and government sectors, this shift invalidates the historical assumption that iOS devices are inherently resistant to all but the most targeted, resource-intensive attacks. The transition to a hit-and-run execution model, where emphasis is placed on immediate data theft followed by automated cleanup, presents us with a severe challenge for traditional digital forensics and incident response (DFIR), as the lack of a persistent binary footprint necessitates a pivot toward real-time behavioral monitoring and aggressive patch management to mitigate risks before exfiltration occurs.
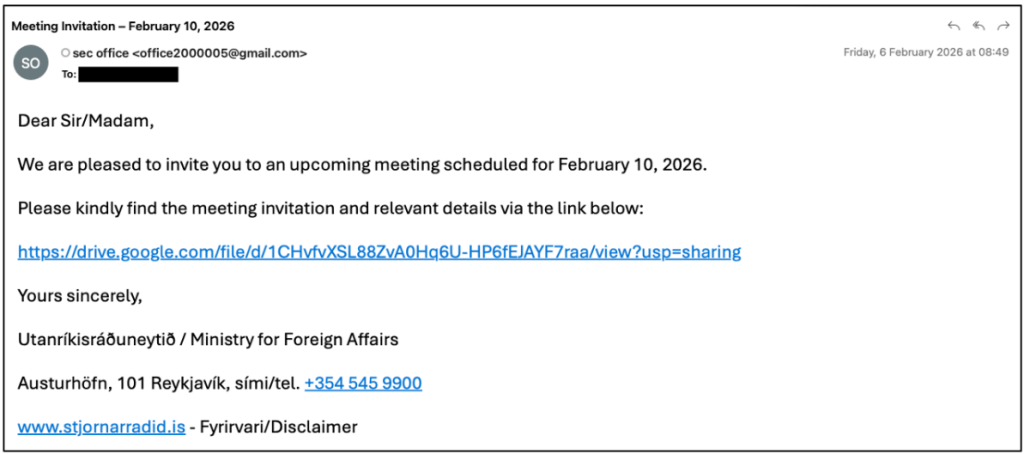
Pro-Russian Actors Impersonate Ukrainian Cyber Agency in Targeting Campaign
The pro-Russian threat actor tracked as UAC-0255 (also tracked as CyberSerp) recently launched a sophisticated phishing campaign impersonating Ukraine’s Computer Emergency Response Team (CERT-UA). The threat actors distributed emails to government agencies, financial institutions, and critical infrastructure providers, warning of an imminent, large-scale Russian cyberattack. To protect their systems, recipients were urged to download a password-protected archive containing what was framed as a specialized security software. In reality, the payload was a remote administration tool (RAT) dubbed AgeWheeze, which grants the threat actors comprehensive control over infected hosts, including the ability to execute commands, manage files, and stream screen content. While the group claimed to have compromised over 200,000 devices, CERT-UA assessed the campaign as largely unsuccessful, with most infections limited to the personal devices of educational staff.
Implications: The transition from spoofing general government ministries to the direct impersonation of CERT-UA is a strategic pivot toward security authority hijacking (possible MITRE alignment here). By weaponizing the very agency responsible for national cyber defense, UAC-0255 exploits a recursive trust loop where urgency is used to bypass traditional skepticism, effectively turning a target’s security consciousness against them. Technically, the deployment of AGEWHEEZE (a Go-based RAT utilizing WebSockets for C2) signals a move toward group-specific, niche tooling meant to evade signature-based detection calibrated for broader state-sponsored malware. Furthermore, the public taunting of CERT-UA and the use of AI-cloned portals show that this is an influence-heavy operation; the primary objective is performative hacktivism, aimed at eroding institutional trust and projecting an image of technical omnipresence, regardless of the actual kinetic or technical success of the malware deployment.
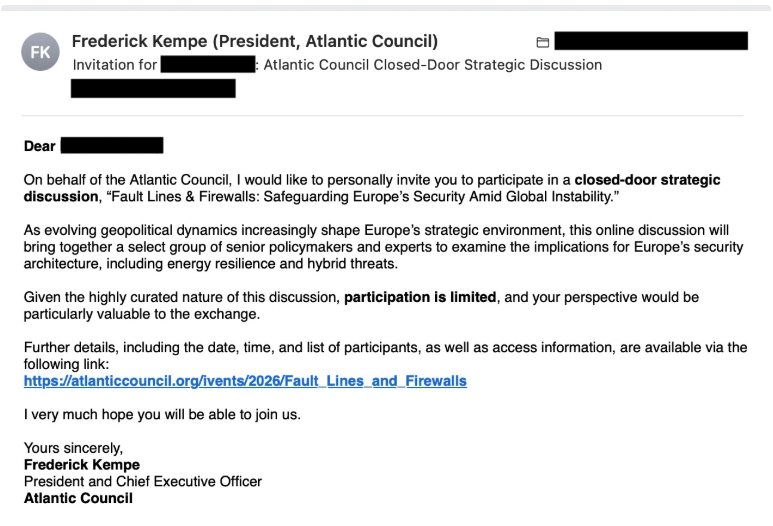
China-Aligned TA416 Resumes Espionage Targeting European Governments
On 1 April 2026, Proofpoint reported the resurgence of the China-linked threat actor TA416 (aka Mustang Panda, RedDelta), which has resumed and expanded its cyber espionage operations targeting European and Middle Eastern government entities, continuing activity observed since at least 2025. The campaign used updated versions of the PlugX RAT, delivered via spear-phishing emails that use contemporary geopolitical themes, like European diplomatic relations and regional security concerns. A notable technical evolution in this activity is the group’s refined use of web beacons for initial target recon and the deployment of a new, simplified Golang loader meant to bypass traditional security perimeters. By using legit, compromised infrastructure for C2, TA416 continues to show high operational tempo and a persistent focus on collecting intel relevant to Chinese strategic interested in Europe.
Implications: For the US DIB and intelligence professionals, the return of TA416 shows the enduring reliance of Chinese APTs on the PlugX ecosystem, despite its age and high signature visibility. The adoption of Golang-based loaders shows a broader trend toward memory-safe, cross-platform languages that complicate reverse engineer and allow for faster iterative development by the adversary. Furthermore, the use of web beacons for pre-exploitation recon shows a sophisticated filtering phase, where the actor ensures a target is high-value before deploying their primary malware, thereby reducing the risk of premature detection by security researchers. TA416’s persistent targeting of European diplomatic channels suggests that organization supporting transatlantic security cooperation must prioritize monitoring for low and slow data exfiltration and strengthen defenses against specialized loaders that may not trigger legacy detections. The expansion into the Middle East, alongside continued European targeting, would suggest a widening scope of collection aligned to global geopolitical priorities. Similar targeting is likely occurring against US government and defense-related organizations, particularly those involved in international coordination, alliance structures, and strategic planning.
Questions or feedback welcome in the comments or via direct message.

Leave a comment