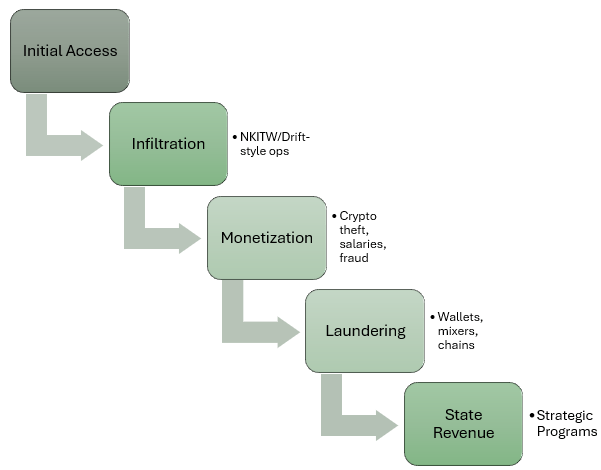
Key Takeaways (tl;dr):
- DPRK cyber activity functions as a coordinated revenue system and not just isolated campaigns
- The Drift compromise shows long-term infiltration using social engineering and trusted access
- Tradecraft mirrors NK IT worker schemes, prioritizing embedded access over external intrusions
- Revenue generated supports NK’s broader strategic programs, including WMD development
Context
North Korean cyber operations are often seen as isolated incidents, a crypto theft here, a phishing campaign there, but in reality, they function as a coordinated financial system. Recent reporting around the compromise of Drift Protocol suggests a broader pattern: DPRK-linked actors are conducting deliberate, long-term operations meant to generate revenue for the state.
On 1 April 2026, Drift Protocol experienced a major exploit resulting in losses estimated at approx. $285 million, with activity later linked to wallets associated with prior NK operations. While large-scale crypto theft attributed to DPRK actors is not new, the mechanics behind this intrusion emphasize and evolution in tradecraft that extends beyond traditional cyber intrusion.
A Six-Month Infiltration
The Drift incident was not the result of a single vulnerability or opportunistic access; it was the culmination of a structured, months-long infiltration effort.
According to Drift’s own reporting, individuals posing as a legitimate quantitative trading firm approached contributors in person at a major crypto conference in late-2025. Over the following six months, DPRK actors maintained ongoing engagement, participating in technical discussions, integrating into the ecosystem, and building credibility through sustained interaction. DPRK actors showed technical fluency, maintained consistent identities, and re-engaged targets across several international events.
The eventual compromise looks to have used multiple vectors introduced through these trusted interactions, including malicious code repos and software distributed under the guise of legitimate tools. In at least one case, simply interacting with a shared repo may have enabled code execution without the user’s awareness.
Attribution is still under investigation, but preliminary assessments indicate overlap with activity associated with UNC4736, a NK state-affiliated group also tracked as AppleJeus.
A Coordinated Financial Ecosystem
The below table shows how several activity types support a coordinated revenue-generation strategy for the DPRK.
| Activity Type | Access Vector | Tradecraft Characteristics | Primary Objective | Typical Op Duration | Target Profile | Example |
|---|---|---|---|---|---|---|
| Cryptocurrency Theft (Lazarus/UNC4736) | Exploitation, supply chain, social engineering | Multi-stage intrusion, custom malware, wallet compromise, laundering via mixers and cross-chain activity | Direct financial gain | Weeks to months | Crypto platforms, DeFi protocols, financial services | Drift Protocol exploit |
| IT Worker Infiltration (NKITW) | Fraudulent employment, identity obfuscation | Use of stolen/forged identities, remote access, sustained presence, salary extraction, potential access enablement | Revenue generation, potential access | Months to years | Private sector companies, including DIB-adjacent orgs | NKIT worker schemes across US firms |
| Targeted Infiltration (Drift-style ops) | Social engineering, relationship building, trusted access | In-person engagement, long-term trust development, technical integration, multi-vector compromise (repos, apps) | Financial theft via trusted access | 6+ months | Crypto ecosystems, developers, platform contributors | Drift Protocol operation |
| Financial Platform Targeting | Phishing, malware delivery, credential harvesting | Credential theft, session hijacking, lateral movement within financial systems | Financial gain, account compromise | Days to weeks | Banks, exchanges, fintech | DPRK-linked phishing campaigns |
| Supply Chain Compromise | Malicious code injection, dependency abuse | Backdoored packages, trusted distribution channels, downstream compromise at scale | Scalable access and monetization | Variable | Software ecosystems, developers, enterprise users | Software/package compromise campaigns |
The significance of this activity extends beyond a single breach. NK cyber operations increasingly resemble a coordinated financial ecosystem comprised of multiple, parallel revenue streams. These include large-scale crypto theft, fraudulent employment schemes involving remote IT workers, and targeted intrusion campaigns against financial platforms and service providers.
While these activities are often analyzed independently, they’re better understood as components of a broader strategy. Each serves the same core objective: generating hard currency for a regime operating under sustained economic sanctions and limited access to the global financial system.
The Drift compromise shows how these operations are converging. Rather than relying solely on technical exploitation, DPRK-linked actors are combining cyber capabilities with long-term social engineering and infiltration. This approach increases the likelihood of success while reducing reliance on zero-day vulnerabilities or higher-risk intrusion attempts; a move in the direction of sophistication.
The model here mirrors patterns observed in NK IT worker (NKITW) schemes, where individuals operating under false or obscured identities secure employment within foreign companies to generate revenues or enable access for intelligence collection. In both cases, the objective is not just the immediate intrusion, but sustained presence within trusted environments that can be used over time for funding NK weapons programs or extracting sensitive intellectual properties from US/allied defense and critical infrastructure organizations.
The Blurred Line Between Insider and Adversary
This model has direct implications for orgs operating in the US defense industrial base (DIB), government, and critical infrastructure sectors.
The tradecraft observed in the Drift operation mirrors patterns seen in NKITW schemes, where adversaries are not attempting to breach networks from the outside (edge devices, public-facing exploits, etc.), but instead position themselves within trusted environments over time, exploiting human processes and social engineering.
This blurs the line between insider threats and external adversaries. Traditional security controls built to detect network intrusions may be less effective against actors who have established legitimate access, built relationships, and integrated into operational workflows.
Implications
DPRK cyber activity should be viewed as strategic and not just criminal or opportunistic. These operations show an increasing sophistication with a level of patience, coordination, and resourcing consistent with state-directed objectives. Financial gain is the mission. Revenue generated through these operations has been repeatedly assessed by US and international authorities as supporting NK’s strategic weapons programs, including its ballistic missile and broader WMD development efforts.
For US orgs, particularly those connected to defense, government, critical infrastructure, and their supply chains, the risk is not limited to direct targeting. It includes indirect exposure through trusted third parties, workforce infiltrations, and participation in ecosystems where adversaries are actively operating.

Leave a comment