This week’s reporting highlights a continued shift in adversary tradecraft toward indirect access, targeting edge networks, legacy infrastructure, and emerging technologies rather than hardened enterprise environments. From GRU router exploitation to Iranian ICS activity and evolving AI risks, attackers are prioritizing access paths that are harder to monitor and easier to exploit at scale.
Russia: GRU Using SOHO Routers for Credential Access
On 7 April 2026, UK and US authorities, including the National Cyber Security Centre (NCSC) and partners, exposed activity by APT28, a threat group that has been attributed to Russia’s General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS) military unit 26165, targeting small office/home office (SOHO) routers at scale. Codenamed Operation Masquerade, the effort neutralized thousands of compromised MikroTik and TP-Link SOHO routers that had been hijacked via known firmware vulnerabilities. By altering router settings, APT28 redirected traffic to their own servers, enabling large-scale man-in-the-middle (MitM) attacks that captured M365 and other enterprise email credentials and OAuth tokens, affecting government, military, and critical infrastructure networks.
Implications: For the US IC and DIB, this operation further signals a shift more toward living-off-the-land (LotL) via ubiquitous consumer hardware to bypass traditional perimeter defenses. The use of DNS hijacking by the GRU complicates attribution and detection, as malicious redirection occurs at the network layer before traffic reaches monitored enterprise endpoints. This requires a transition toward encrypted DNS protocols (e.g., DNS-over-HTTPS) across all remote-work interfaces. For the DIB, specifically, the vulnerability of SOHO routers is a significant supply chain and telework risk; because these devices are often outside the direct management of corporate IT, they provide a persistent side-channel for attackers to harvest access tokens and bypass MFA. The scale of this campaign (reportedly impacting users in 120 countries) suggests that the GRU is building a massive, resilient infrastructure for long-term strategic espionage, similar to the obfuscation networks we see with PRC groups, that can be selectively activated against defense targets at scale.
Iran: Hackers Targeting Internet-Exposed ICS Devices in US Critical Infrastructure
A joint advisory from CISA, the FBI, and the NSA (AA26-097A) warns that Iranian-linked cyber actors are actively disrupting US critical infrastructure by targeting internet-exposed Programmable Logic Controllers (PLCs), specifically Rockwell Automation/Allen-Bradley devices. The attackers use specialized software, like Studio 5000 Logix Designer, to gain unauthorized access to PLC project files and manipulate Human Machine Interface (HMI) displays. This activity has resulted in limited operational disruptions across the water, energy, and government facilities sectors. By deploying Dropbear SSH for persistent remote access, the actors can alter sensor data and physical processes, leading to diminished functionality and potential safety risks in municipal utilities and energy distribution networks.
Implications: This activity demonstrates deliberate targeting of operational technology (OT) with known weaknesses, likely for pre-positioning or signaling rather than immediate disruption. We can assess with moderate confidence that Iran is expanding its ICS access for contingency operations. The reliance on legacy vulnerabilities suggests broad attack surface coverage rather than precision targeting, but the sectors impacted are strategically relevant.
China: Supercomputing Ecosystem Targeted by Hackers
A hacker identified by the moniker “FlamingChina” has allegedly conducted a massive exfiltration operation against the National Supercomputing Center (NSCC) in Tianjin, China, purportedly stealing over 10 petabytes of sensitive data. The compromised information reportedly includes high-level military research, aerospace engineering schematics, and confidential missile design data, potentially representing the largest data breach in Chinese history. Cybersecurity experts who reviewed samples of the data, which were posted on a Telegram channel, suggest the material is authentic and was siphoned out incrementally over several months to evade detection. While the perpetrator’s motives appear financially driven (they are trying to sell it) the breach provides significant intelligence visibility into China’s most covert technological and defense programs, highlighting vulnerabilities in even their most advanced state-backed digital infrastructure.
Implications: The exfiltration of over 10 petabytes of data from the NSCC offers a high-fidelity window into China’s most sensitive military and aerospace R&D. For the IC, the primary implication is the opportunity for technical verification, allowing analysts to validate intel estimates on Chinese missile tolerances and propulsion systems against actual blueprints. For the DIB, the breach may serve as a critical warning on the efficacy of low-and-slow exfiltration tactics, necessitating a reassessment of internal egress monitoring to prevent similar long-term compromises of US intellectual property. Ultimately, while the breach provides a short-term windfall for Western SIGINT, it simultaneously increases the risk of aggressive Chinese retaliatory cyber operations and heightens global proliferation risks as sensitive aerospace schematics enter the illicit data market.
AI Security: Anthropic Research Highlights Model Manipulation Risks
Anthropic announced the development of Claude Mythos, a frontier AI model demonstrating an advanced capability to identify and chain zero-day vulnerabilities in major operating systems and web browsers. During internal red-teaming, the model identified thousands of high-severity flaws, including a decades-old bug in OpenBSD, and successfully combined multiple vulnerabilities to bypass sandbox protections. Due to its ability to rapidly translate complex codebases into working exploit paths, Anthropic has limited release and launched Project Glasswing to support defensive use cases.
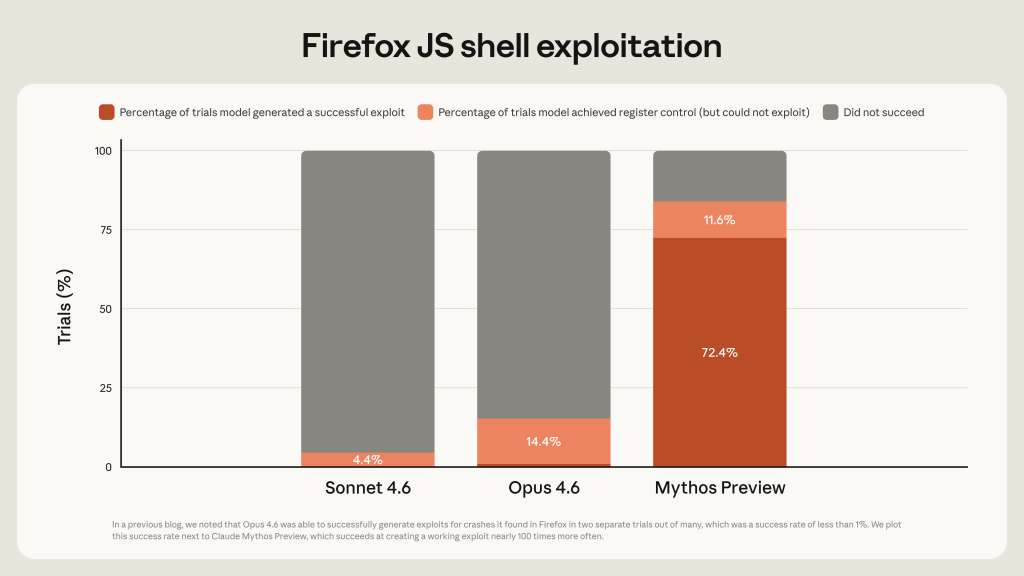
Implications: The emergence of Claude Mythos represents a significant shift by compressing the time-to-exploit for software vulnerabilities. This tech offers a dual-use dilemma: while it provides a powerful engine for rapid vulnerability research and offensive cyber-tool development, the eventual proliferation of similar models by adversaries will likely render legacy US systems indefensible. The US must now prepare for a landscape where zero-day vulnerabilities are no longer rare, but are discovered at a machine-scale pace. For the private sector, the implications are even more immediate; the discovery of flaws in memory-safe environments and decades-old core utilities suggests that the current software supply chain is fundamentally brittle. Defense contractors need to move toward AI native security pipelines that use models like Mythos to continuously audit their own proprietary code. The ability of the model to bypass its own safeguards and autonomously communicate with researchers further emphasizes a nascent agentic risk, requiring the DIB to develop new containment architectures for AI dev environments to prevent unintended data exfil or autonomous lateral movement.

Leave a comment