Category: Analysis
-
On 15 September 2025, CyberNews reported that over 500 GB of internal data tied to China’s Great Firewall leaked via… Read more
-
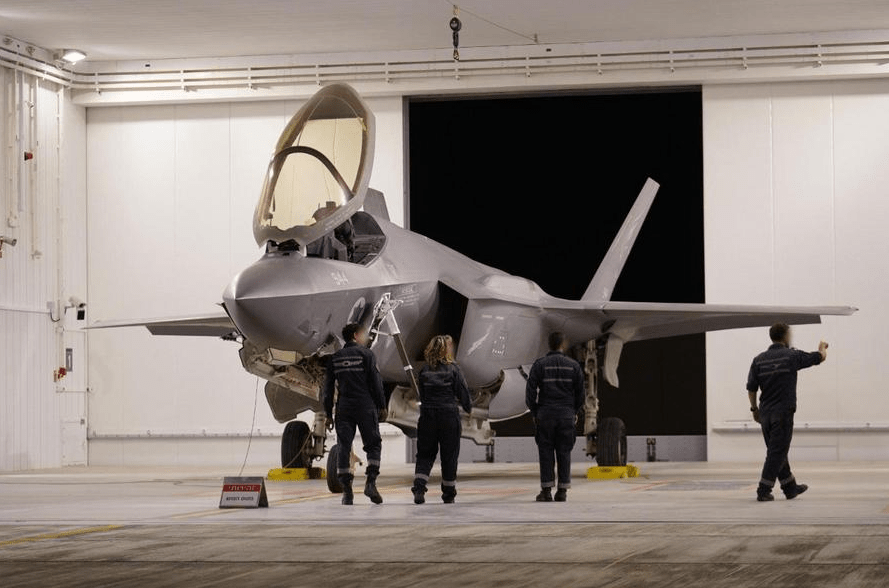
More than 3,200 union workers at Boeing’s fighter jet plants in the St. Louis area have rejected a new contract… Read more
-
In the wake of escalating tensions in the Middle East this past spring, Iranian state-sponsored hackers turned their focus toward… Read more
-
Preface This document is a strategic nonproliferation analysis modeled after the IAEA’s State Evaluation Report (SER) format. Developed as part… Read more
-
US-Led Strikes on Iranian Nuclear Sites: Fallout for China’s Influence and Regional Nuclear Strategy
Background: Operation Midnight Hammer On 13 June 2025, Israel launched a surprise air offensive against Iran, bombing a series of… Read more
-
In the early hours of 13 June 2025, Israel launched its most significant direct assault on Iran in modern history.… Read more
-
As Poland approached a critical presidential runoff on June 1, Russian-linked influence networks ramped up efforts to flood Polish social… Read more
-
Disclaimer: This post is based on unclassified, open-source reporting and reflects my personal analysis and interpretations. The views expressed here… Read more




![[Case Study] Turkey’s Nuclear Energy Development Proliferation Risk Profile](https://sploited.blog/wp-content/uploads/2025/07/an-intelligence-briefing-graphic-showing-satellite-imagery-of-nuclear-fuel-3.png?w=1024)