Category: Security
-
This week’s reporting highlights a continued shift in adversary tradecraft toward indirect access, targeting edge networks, legacy infrastructure, and emerging… Read more
-
Key Takeaways (tl;dr): Context North Korean cyber operations are often seen as isolated incidents, a crypto theft here, a phishing… Read more
-
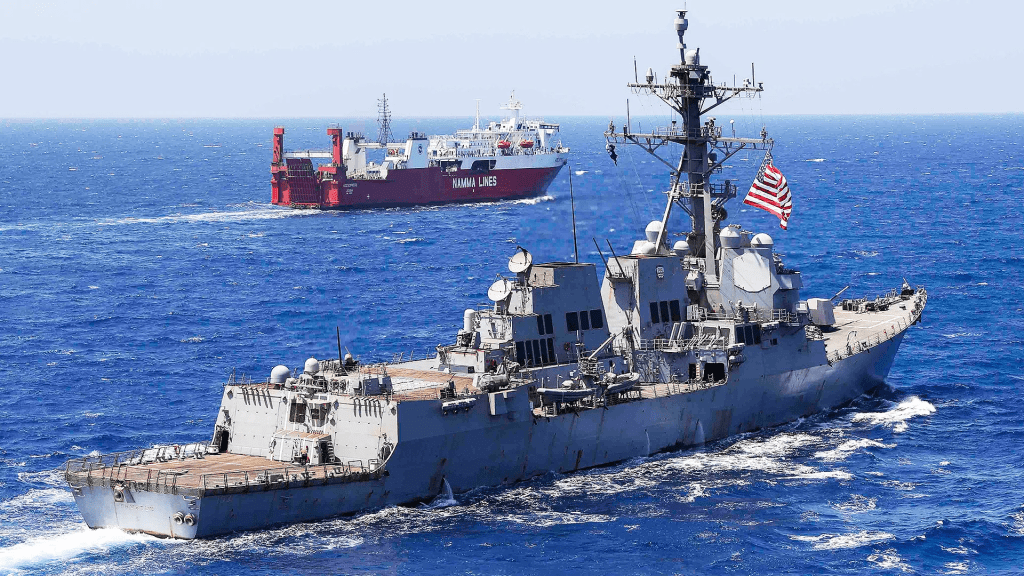
This week’s roundup highlights state-sponsored cyber activity targeting government, critical infrastructure, and defense-related organizations, with a focus on strategic intent… Read more
-
This weekly roundup is meant to highlight key cyber and geopolitical developments observed over the past several days, focusing on… Read more
-
The modern software supply chain is built on a foundation of implicit trust; a trust that users and systems place… Read more
-
In late-December 2025, the Polish energy sector was targeted by a coordinated series of destructive cyberattacks using a new malware… Read more
-
BLUF: The Iranian regime is transitioning from reactive crisis management to a proactive digital isolation strategy to secure domestic stability.… Read more