Category: Threats
-
In the wake of escalating tensions in the Middle East this past spring, Iranian state-sponsored hackers turned their focus toward… Read more
-
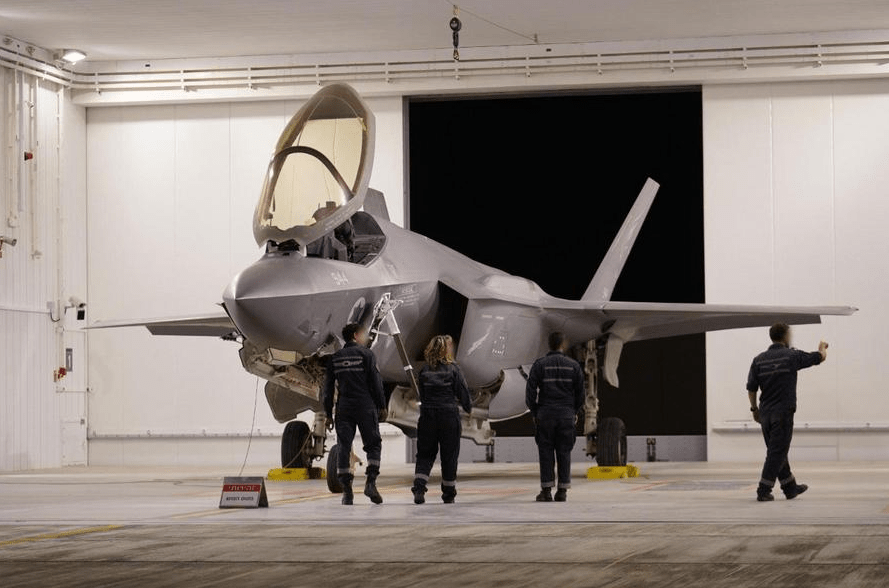
US-Led Strikes on Iranian Nuclear Sites: Fallout for China’s Influence and Regional Nuclear Strategy
Background: Operation Midnight Hammer On 13 June 2025, Israel launched a surprise air offensive against Iran, bombing a series of… Read more
-
In the early hours of 13 June 2025, Israel launched its most significant direct assault on Iran in modern history.… Read more
-
As Poland approached a critical presidential runoff on June 1, Russian-linked influence networks ramped up efforts to flood Polish social… Read more
-
Disclaimer: This post is based on unclassified, open-source reporting and reflects my personal analysis and interpretations. The views expressed here… Read more
-
Microsoft Threat Intelligence has surfaced a new Russia-affiliated cyber actor: Void Blizzard, also tracked as LAUNDRY BEAR. Active since at… Read more
-
Disclaimer: This research uses data derived from open-source materials like public intelligence assessments, government publications, and think tank reports. This report… Read more
-
Rethinking Russian Influence Operations in the Age of Weaponized Visibility Earlier this month, Sweden’s Psychological Defence Agency and Lund University… Read more
-
The Digital Guerrilla When you think of cyber warfare, you often imagine digital equivalents of tanks, missiles, and grand battles… Read more
-
Summary Between Jan and Apr 2025, suspected Russian FSB-linked threat group COLDRIVER delivered LOSTKEYS malware using a fake CAPTCHA to… Read more



![[Deep Dive] Cyber Tactics and Counterterrorism Post-9/11](https://sploited.blog/wp-content/uploads/2025/05/create-a-featured-image-for-a-blog-post-focusing-on-3.png?w=1024)