The Digital Guerrilla
When you think of cyber warfare, you often imagine digital equivalents of tanks, missiles, and grand battles between major powers. In reality, however, the cyber conflict we see today looks less like Normandy and more like a slow-burning insurgency.
State-sponsored actors, whether they be from Russia, China, Iran, or North Korea, rarely go toe-to-toe with superior Western cyber defenses in a direct, conventional fight. Instead, they operate in the shadows, using asymmetric tactics meant for low-cost, high-yield disruption. Their methods resemble the playbook of guerrilla fighters throughout history: blend in, strike vulnerable targets, and exploit the defender’s size and rigidity.
In today’s post, I’ll unpack how these cyber operations mirror classic guerrilla warfare and why this analogy is so interesting and matters for defenders.
Guerrilla Warfare 101
It’s all about fighting smarter, not harder. It’s the art of the weak harassing the strong. Following the great stalemates of trench warfare in WWI, insurgent groups have leveraged mobility, surprise, and intimate knowledge of the terrain to outmaneuver larger, better-equipped militaries.
Characteristics of guerrilla warfare include:
- Asymmetry: Small groups using unconventional methods to challenge superior foes.
- Deniability: Fighters blend into civilian populations, making attribution and retaliation tougher.
- Hit-and-run tactics: Ambushes, sabotage, quick raids, always moving.
- Psychological ops: Targeting public morale, misinformation.
- Terrain advantage: Mastery of local geography to evade and frustrate conventional forces.
Sounds familiar, right? Swap out “fighters” for “APT groups“, “civilian populations” for “cybercriminal groups“, and “terrain” for “network infrastructure“, and you’ve got a pretty solid picture of today’s cyber landscape.
Guerrilla Tactics in Action: State-Sponsored Cyber Threats
Asymmetry in the Digital Domain
State-sponsored groups like Russia’s APT28 and APT29 or North Korea’s Lazarus Group rarely match US or allied cyber capabilities head-on. They exploit the cost asymmetry. For a few thousand dollars in phishing kits, compromised VPNs, leased botnets, or commercial malware, they can inflict millions in damages, steal sensitive data, or shape public narratives. The defender’s dilemma? Defending every endpoint and supply chain vector costs exponentially more than launching simple, repeatable attacks.
Deniability and Proxy Warfare
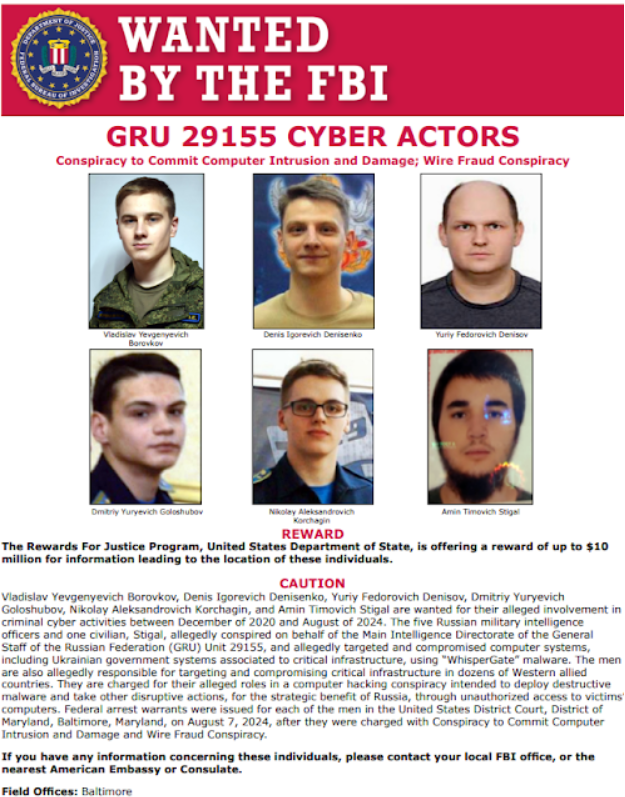
Just as guerrillas hide among civilians, cyber operators mask their identities using compromised infrastructure, false flags, or contracting work out to cyber criminal elements and impressionable anarchists in the case of Russian GRU’s Unit 29155 who incite anarchy and sabotage through various Telegram channels to Ukrainian youth. North Korea’s use of 3rd party IT freelancers to infiltrate Western companies is another prime example. The plausible deniability muddies attribution, delays response, and allows our adversaries to operate with relative impunity.
Hit-and-Run in Cyberspace
Watering hole attacks, defacements, and smash-and-grab data theft mirror the guerrilla’s ambush. Breach a vulnerable vendor, pivot to the target, exfiltrate quickly, and vanish while defenders are left scrambling. These aren’t prolonged sieges, they’re opportunistic raids meant to probe weaknesses and sow chaos.
Information Warfare as PsyOps
Iranian and Russian cyber units have elevated disinformation to an art form. Influence operations targeting elections, societal divisions, or corporate reputations function as digital equivalents of guerrilla psychological operations. The goal isn’t always tangible damage; sometimes it’s just to erode trust and create confusion or panic.
Mastering the Digital Terrain
In guerrilla conflicts, knowing the terrain is everything. In cyberspace, that “terrain” includes compromised networks, 3rd party vendors, poorly monitored endpoints, and the dark web. State-sponsored groups map this terrain meticulously, identifying soft targets and exploiting global infrastructure for cover.
Some Case Studies: Cyber Guerrilla Warfare in Practice
In 2025, there are now plenty of examples to pull from but some of the more recent, notable cases include:
Russia’s (FSB) COLDRIVER/Callisto/Star Blizzard
Operating between cyberespionage and influence, this group exemplifies cyber guerrilla tactics. With recent reporting detailing their persistent targeting of Western NGOs, think tanks, and academia reflects a strategy of sustained harassment. They focus on undermining soft targets, shaping narratives, and stealing sensitive (not always classified) information that feeds broader geopolitical campaigns.
North Korea’s IT Worker Fraud
The DPRK has combined traditional APT activities with an insurgent-style infiltration campaign: fraudulent IT workers securing remote jobs at Western firms. Once inside, these operatives act as insider threats with direct access to networks, sidestepping conventional perimeter defenses. This tactic parallels how insurgents embed within civilian populations to evade detection and execute attacks from within. In this case, funding the regime’s weapons programs, among other motivations.
Iran’s APT33/35/42
Iranian threat groups excel at opportunistic targeting, often focusing on vulnerable sectors like oil & gas, transportation, and academia. Their attacks prioritize disruption, espionage, and influence, mirroring guerrilla strategies of infrastructure sabotage and psychological impact over decisive victories.
Volt Typhoon: An Occupational Model
China’s Volt Typhoon operations showcase a more sophisticated “occupation” model. Rather than smash-and-grab, their campaigns are long-term entrenchments in U.S. critical infrastructure, designed for persistent access and latent sabotage potential. This is less hit-and-run, more like guerrilla fighters establishing fortified zones in contested territory.
Why the Guerrilla Warfare Analogy Matters
Understanding cyber threats through the lens of guerrilla warfare reframes how we think about defense and deterrence.
- Misaligned Defenses: Conventional cyber defenses are analogous to defending cities with large armies while insurgents roam freely in the countryside. Static defenses are insufficient against agile, persistent adversaries.
- Deterrence is Harder: You can deter a nation’s military with superior firepower. Deterring a deniable, decentralized cyber guerrilla force is a different challenge.
- Hybrid Warfare Context: These cyber guerrilla tactics don’t exist in a vacuum. They’re part of broader hybrid strategies, supporting kinetic operations, diplomatic pressure, or internal destabilization efforts.
Mitigation?
This is tough one as mitigation against guerrilla tactics requires more than simply building bigger walls or buying more security tools. Some things worth considering:
- Persistent threat hunting
- Implement honeypots
- Coordination/collaboration across government, private sector, and civil society
- Publicly naming and sanctioning enablers
Tactics Snapshot
- Phishing (social engineering)
- Credential Harvesting (Supply chain raids)
- Watering Hole Attacks (sabotaged Infrastructure)
- Supply Chain Subversion (indirect targeting)
- Wiper Malware (destructive sabotage)
Conclusion
Guerrilla warfare didn’t disappear with the end of colonial insurgencies or Cold War proxy wars. It evolved and found a new battleground on the web. Today’s state-sponsored cyber operations mirror the asymmetric tactics of historical insurgencies in that they’re cheap, deniable, persistent, and designed to frustrate superior foes. For defenders like us, recognizing this parallel is less academic and more essential for adapting strategy, resource allocation, and useful threat modeling.
The digital guerrilla is no longer just a rebel in the jungle. They’re a sanctioned asset, behind a keyboard, operating in the blurred space between espionage, sabotage, and information warfare.