In the wake of escalating tensions in the Middle East this past spring, Iranian state-sponsored hackers turned their focus toward a new frontier: US critical infrastructure.
From May through June 2025, cybersecurity telemetry revealed a 133% surge in Iran-attributed cyber activity targeting US industrial and operational technology (OT) environments. These campaigns hit transportation and manufacturing sectors, but energy and water infrastructure remain long-standing targets. While espionage remains a primary objective, the evidence increasingly suggests Iran is preparing for more overt disruption.
Strategic Escalation
Iran’s cyber posture has always mirrored its geopolitical environment. In Spring 2025, that meant responding to Israeli and US airstrikes with asymmetric cyber operations. Groups like APT33 (Elfin), APT34 (OilRig), and MuddyWater (Static Kitten) ramped up traditional espionage, while more aggressive actors like CyberAv3ngers and Fox Kitten (tied to recent Pay2Key.I2P ransomware operations) pursued OT-focused sabotage and ransomware deployment.
Iran’s messaging through pseudo-hacktivist fronts and deepening ties with ransomware operators clearly framed this activity as retaliation for “Western aggression.” That framing is part of a broader Iranian cyber doctrine that views critical infrastructure compromised as a form of coercion and deterrence.
In parallel with APT activity, pro-Iranian hacktivists ramped up operations against US defense and critical infrastructure sectors. Groups like “Mr. Hamza” claimed responsibility for defacing and leaking data tied to defense contractors, including Raytheon technologies (RTX), following US involvement in strikes against Iranian facilities. While attribution remains murky, these operations often mirror Iranian state objectives and timelines, suggesting coordination or at least ideological alignment. The targeting of US DIB entities serves Tehran’s broader goal of projecting reach and retaliation across both digital and strategic domains.
Pre-Positioning
Iran’s shift toward OT environments is the most significant development.
- MuddyWater and APT33 continued to exfiltrate intellectual property from manufacturing and defense-adjacent industries.
- CyberAv3ngers targeted water control systems and other ICS devices with their custom malware, IOControl, discovered embedded in US and allied OT environments.
- Fox Kitten evolved into a ransomware-as-a-service operator with an 80% (up from 70%) profit-share for affiliates targeting the US or Israel.
Alongside collecting information, these actors are also establishing persistence. In many cases, backdoors were quietly planted and left dormant; signaling an intent for future activation should the need arise.
| Actor | Affiliation | Focus | Objective |
|---|---|---|---|
| MuddyWater | MOIS | Aerospace & Defense, Utilities, Gov, Civil & NGOs | Espionage |
| APT33 | IRGC | Aerospace & Defense, Energy, Gov, Healthcare | Espionage and Access |
| CyberAv3ngers | IRGC | Water, ICS, Finance | Disruption |
| Fox Kitten | Unkown | IT/OT Gateways | Ransomware-as-a-service |
| OilRig | MOIS | Finance, Gov | Credential Theft |
Implications for the US DIB
Iran’s campaigns are displaying a willingness to target logistics, aerospace, and manufacturing suppliers that support US and Israeli defense sectors. The Defense Industrial Base (DIB) should expect more of this; not only from state-sponsored actors, but from criminal or hacktivist affiliates acting on behalf of Iran’s IRGC or MOIS cyber arms.
Some immediate implications:
- DIB contractors should hunt for Iranian TTPs and malware like IOControl and DNSpionage.
- OT segmentation, remote access policies, and endpoint hygiene are foundational.
- Incident response (IR) planning must include scenario-based escalation modeling: what happens if the access Iran gains today becomes a wiper event tomorrow?
US Response: Shields Up
Initially, the federal response may have felt quieter than prior cyber alerts like those during the Ukraine conflict but the signals were still there.
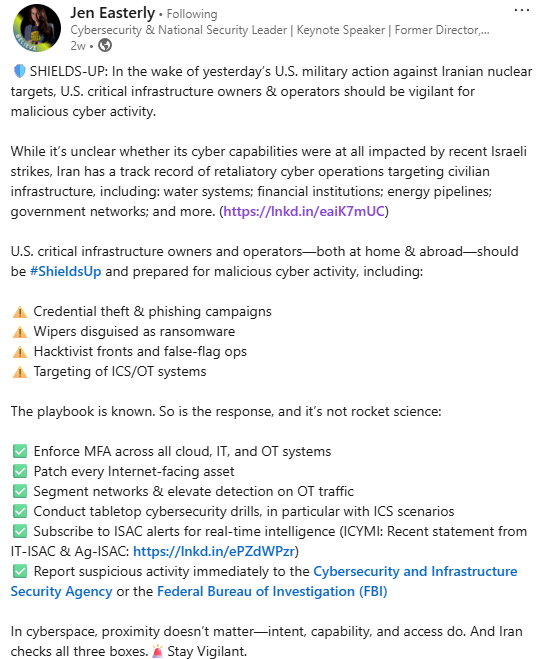
On LinkedIn, Jen Easterly, former CISA Director, reactivated the Shields Up mantra within hours of US strikes on Iranian nuclear sites. Her post explicitly warned US critical infrastructure operators to expect:
- Credential theft and phishing
- ICS-specific malware
- Wipers masquerading as ransomware
- Propaganda-laced hacktivist campaigns
Easterly urged sectors to segment OT networks, patch internet-facing systems, enforce MFA, rehearse ICS isolation, and actively monitor ISAC channels.
The various critical infrastructure-related ISACs followed suit. And while no single campaign bannered over the response, the defense posture matched the moment.
So What’s Next?
Iran’s recent activity represents a shift in focus, not necessarily a shift in capability. The targeting of OT environments and critical infrastructure may reflect aspirational doctrine as much as operational readiness. While there’s no conclusive evidence that Iranian actors have staged disruptive payloads in U.S. networks, the direction of their targeting and tooling, particularly the development of ICS and OT-specific malware, suggests a growing interest in operational disruption, and not just information gathering.
For the US defense and critical infrastructure communities, this creates a clear mandate to prepare for the next phase before it arrives.
- Monitor beyond the perimeter: Iranian threat actors have historically gained access through default credentials, exposed devices, and lateral movements through flat networks.
- Expect dual-use operations: Intelligence collection and pre-positioning are not mutually exclusive.
- Reassess assumptions: Iranian groups are traditionally viewed as less sophisticated than Russian or Chinese APTs, but recent coordination and tooling suggest they’re evolving quickly.
In short, we’re seeing a doctrinal pivot. Iran is exploring offensive options in OT environments, and testing how far it can go without triggering escalation. This makes detection, attribution, and sector-wide coordination more important than ever.
References
https://www.nozominetworks.com/blog/threat-actor-activity-related-to-the-iran-conflict
https://claroty.com/team82/research/inside-a-new-ot-iot-cyber-weapon-iocontrol
https://therecord.media/iran-state-backed-hackers-industrial-attacks-spring-2025