Disclaimer: This post is based on unclassified, open-source reporting and reflects my personal analysis and interpretations. The views expressed here are my own and do not represent the views or positions of my employer.
In a previous post, I detailed GRU Unit 29155’s role in physical sabotage campaigns across Europe, from the Skripal poisoning to the Czech arms depot blasts. For years, their operations reflected a legacy of Cold War-era tradecraft. Covert, kinetic, and plausibly deniable.
But according to a new investigation from The Insider, Unit 29155 has undergone a major transformation. While their physical sabotage capabilities remain intact, they have expanded into the cyber domain, developing a set of offensive capabilities that go far beyond what most attributed to this unit.
This evolution has implications not only for Ukraine but for NATO supply chains, digital infrastructure, and future hybrid conflicts.
Cyber Attacks
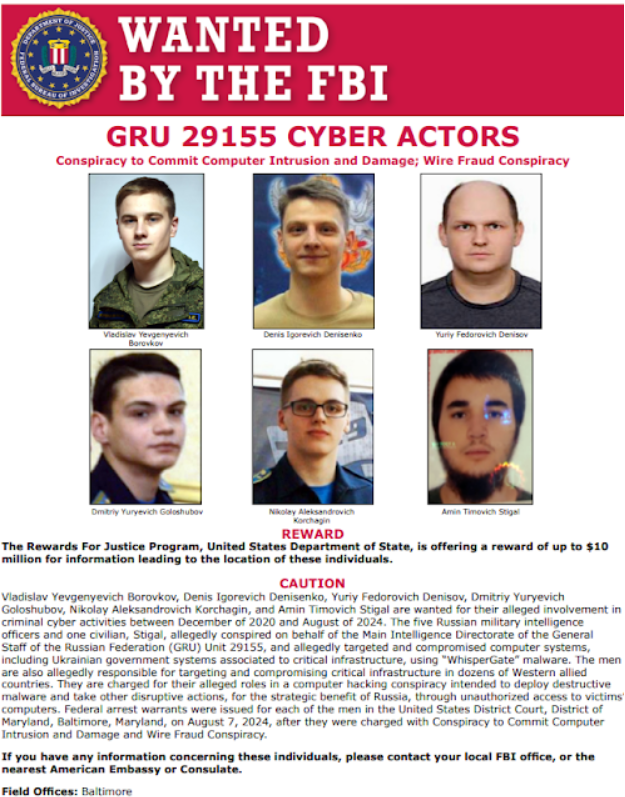
The reporting confirms what many in the threat intelligence space have suspected. Unit 29155 is no longer limited to physical acts of disruption. In 2022, the group ran the WhisperGate operation in Ukraine, using destructive malware to damage government systems and leak personal data. The intent was not just disruption. It was psychological destabilization.
This operation was structured and deliberate. The malware wiped systems while the data leaks created distrust. This fits Russia’s broader approach to hybrid warfare, where technical, cognitive, and physical effects are coordinated for maximum pressure.
Disinformation Campaigns
Unit 29155 also operated false flag personas like Anonymous Poland. These were used to publish disinformation that undermined trust between Ukraine and its Western partners. This was not unsophisticated trolling. It was part of a campaign using multilingual content and coordinated narratives.
In one example, the group reportedly collaborated with Bulgarian journalist Dilyana Gaytandzhieva to publish stolen material. This gave the operation a veneer of journalistic legitimacy. Russia has long used this kind of media laundering to amplify leaks, but seeing it connected to Unit 29155 shows their deeper involvement in the information space.
Hacker Recruitment
This evolution started more than a decade ago. Around 2012, the GRU began recruiting programmers and hackers through online forums and competition platforms. They focused on individuals who could operate quietly, build offensive tools, and maintain strong operational security.
Some of these actors developed malware, access frameworks, and data exfiltration tools that supported both espionage and sabotage. This is the convergence of cybercrime tradecraft and military doctrine. Unit 29155 has grown into a force that can operate in the digital domain with the same intent and effect as their physical missions.
NATO Supply Disruption
The investigation also highlights the unit’s interest in transportation and logistics networks, particularly in countries like Poland. This is a strategic move. It targets the rear areas that support Ukraine’s defense by interfering with how weapons and supplies reach the front lines.
Instead of blowing up rail lines, the modern version might involve tampering with scheduling software, triggering false alarms, or planting disruptive code that causes bottlenecks. The outcome is the same. Slow the response. Introduce uncertainty. Force decision makers to question the integrity of their support systems.
This aligns closely with Russian military thinking. Create friction, delay, and confusion through minimal but high impact actions.
Analyst Comments
This isn’t a new threat; it’s a mature one. GRU Unit 29155 has evolved from a physical sabotage unit into a hybrid operations group. Their capabilities now span cyber access, information warfare, and physical disruption. All under the same command structure.
For security professionals, this should change how we think about attribution and intent. A single unit may now be responsible for an email phishing campaign, a leaked set of government documents, and a compromised transportation system. That complicates response planning and forces a more integrated intelligence posture.
In my opinion, cyber sabotage is no longer the prelude to conflict. In many cases, it is the conflict.
References
https://theins.press/en/inv/281731