This week’s reporting centers on access and scale. State-aligned actors are targeting people, platforms, and partnerships to expand reach, from Chinese phishing campaigns against journalists to DPRK operations exploiting developers and the Web3 sector, alongside growing Russia–North Korea alignment.
China Targets Journalists in Sustained Phishing Campaign
On 27 April 2026, Citizen Lab reported a sophisticated digital transnational repression (DTR) campaign conducted by two China-aligned actors, GLITTER CARP and SEQUIN CARP, targeting journalists and diaspora communities. Operating with infrastructure active since at least 2023, these actors used specialized phishing tactics, ranging from high-volume credential theft to high-fidelity social engineering, to impersonate media organizations like the International Consortium of Investigative Journalists (ICIJ) and co-opt sensitive narratives for intelligence collection. By targeting reporters and activists across the Tibetan, Uyghur, Taiwanese, and Hong Kong diasporas, the campaign aims to suppress cross-border dissent and monitor those documenting the state’s human rights record.
Analyst Comment: The separation between clusters and tradecraft suggests some level of structure behind the scenes, likely enabling multiple campaigns to run at the same time without drawing too much attention. Using trusted organizations as cover adds another layer, making it harder for journalists and researchers to know what’s legitimate. Over time, that kind of pressure erodes trust and slows down the flow of information. For analysts, it reinforces how much of this activity is centered on identity and access, with collection happening quietly in the background rather than through loud or disruptive operations.
China-Linked Hacker Extradited to US Over HAFNIUM Activity
On 27 April 2026, Xu Zewei, a 34-year-old Chinese national, appeared in a Houston federal court following his extradition from Italy to face a nine count indictment for state-sponsored cyber intrusions. Operating under the direction of the Shanghai State Security Bureau (SSSB) while employed by the private “enabling” firm Shanghai Powerock Network Co. Ltd., Zu is alleged to have participated in the HAFNIUM campaign, which compromised over 12,700 US organizations. The charges detail specific operations between 2020 and 2021 that targeted COVID-19 research at US universities and exploited Microsoft Exchange Server vulnerabilities to exfiltrate data on US policy makers.

Analyst Comment: This case serves as yet another example of China’s continued reliance on a hybrid model, pairing state direction with private sector operators to scale intrusion activity while maintaining some distance from direct attribution. Targets tied to COVID-19 research and policy reflect how these operations align with Chinese national-level priorities.
Extradition remain limited and largely depend on travel outside China, so the broader deterrent impact is minimal. That said, they introduce real personal risk for operators, especially in jurisdictions willing to cooperate with the US.
Russia and North Korea Formalize Long-Term Military Cooperation
During the third high-level strategic dialogue in Moscow, Russia and North Korea formalized an agreement to expand long-term military cooperation, deepening the bilateral defense relationship established during President Putin’s June 2025 visit to Pyongyang. The agreement likely addresses mutual defense logistics, technology transfers, and potential troop deployments, following reports of North Korean personnel assisting Russian efforts in the conflict in Ukraine. While Russia frames the pact as a “comprehensive strategic partnership” aimed at stabilizing Northeast Asia, international observers view the alignment as a direct challenge to the Western-led security architecture. The deal provides Russia with a critical pipeline for conventional munitions and manpower, while North Korea gains significant leverage through access to Russian aerospace technology and food security assistance, further complicating denuclearization efforts on the Korean Peninsula.

Analyst Comment: Russia gains a steady source of munitions and manpower, while North Korea benefits from access to advanced tech and much needed economic support. That exchange creates a mutually reinforcing relationship that is likely to persist beyond the conflict in Ukraine.
Over time, this cooperation increases the risk of capability transfer in areas like missile development, space, and military aviation. It also adds complexity for Western policymakers, as pressure applied to one actor will undoubtedly have second-order effects through the other.
DPRK-Linked BlueNoroff Targets Web3 with AI-Driven Lures
Arctic Wolf Labs has identified a sophisticated intrusion campaign attributed to BlueNoroff, a financially motivated subgroup of the North Korean Lazarus Group, targeting the Web3 and cryptocurrency sectors. The attack lifecycle begins with high-fidelity social engineering, where actors impersonate reputable figures to deliver manipulated Calendly invites that redirect victims to typo-squatted Zoom domains. During these fake meetings, the threat actors employ a self-reinforcing AI pipeline, combining exfiltrated webcam footage from prior victims with deepfake imagery to create highly convincing lures for subsequent targets. Technically, the campaign uses ClickFix clipboard injection and fileless PowerShell-based implants to bypass traditional antivirus defenses, enabling full system compromise in under five minutes. This industrialized approach to credential and cryptocurrency exfiltration (spanning over 20 countries) supports the group’s ability to combine mature technical tradecraft with recursive social engineering to maintain a scalable and persistent threat to the global financial ecosystem.
Analyst Comment: This campaign shows how far social engineering has come. BlueNoroff is putting effort into building believable interactions, using AI and recycled victim data to make each engagement more convincing; something we’ve seen from several clusters of DPRK activity, including fraudulent IT workers. The result here is a feedback loop where every successful compromise improves the next attempt.
The technical side supports speed; fileless execution and clipboard injection allow the actors to move from initial contact to full compromise fairly quickly, limiting the window of discovery or user hesitation.
Identity and trust are still the easiest way in and these campaigns are becoming more repeatable and scalable, especially as AI lowers the effort required to build convincing lures. As defenders, the focus shifts to using AI for detection and validation at scale, not just assuming users can spot this level of deception.
DPRK-Linked Void Dokkaebi Uses Fake Interviews to Spread Malware
Trend Micro researchers have documented a targeted campaign by Void Dokkaebi (historically associated with North Korean operations) that uses fraudulent job interview lures to compromise developers and the Web3 sector. The attack chain begins with sophisticated social engineering, where threat actors invite targets to participate in technical assessments that require the download and execution of code from GitHub or GitLab repositories. These repositories contain malicious npm packages or hidden scripts that deploy a multi-stage malware payload, including the Wasabi and DogeRAT families, designed for persistent access and credential exfiltration. By leveraging the inherent trust in developer workflows and common open-source platforms, Void Dokkaebi demonstrates a high level of operational maturity, focusing on supply-chain contamination and the theft of intellectual property and digital assets. This tactic underscores the continued evolution of North Korean-linked threat actors in exploiting niche professional communities through highly personalized, high-fidelity lures.
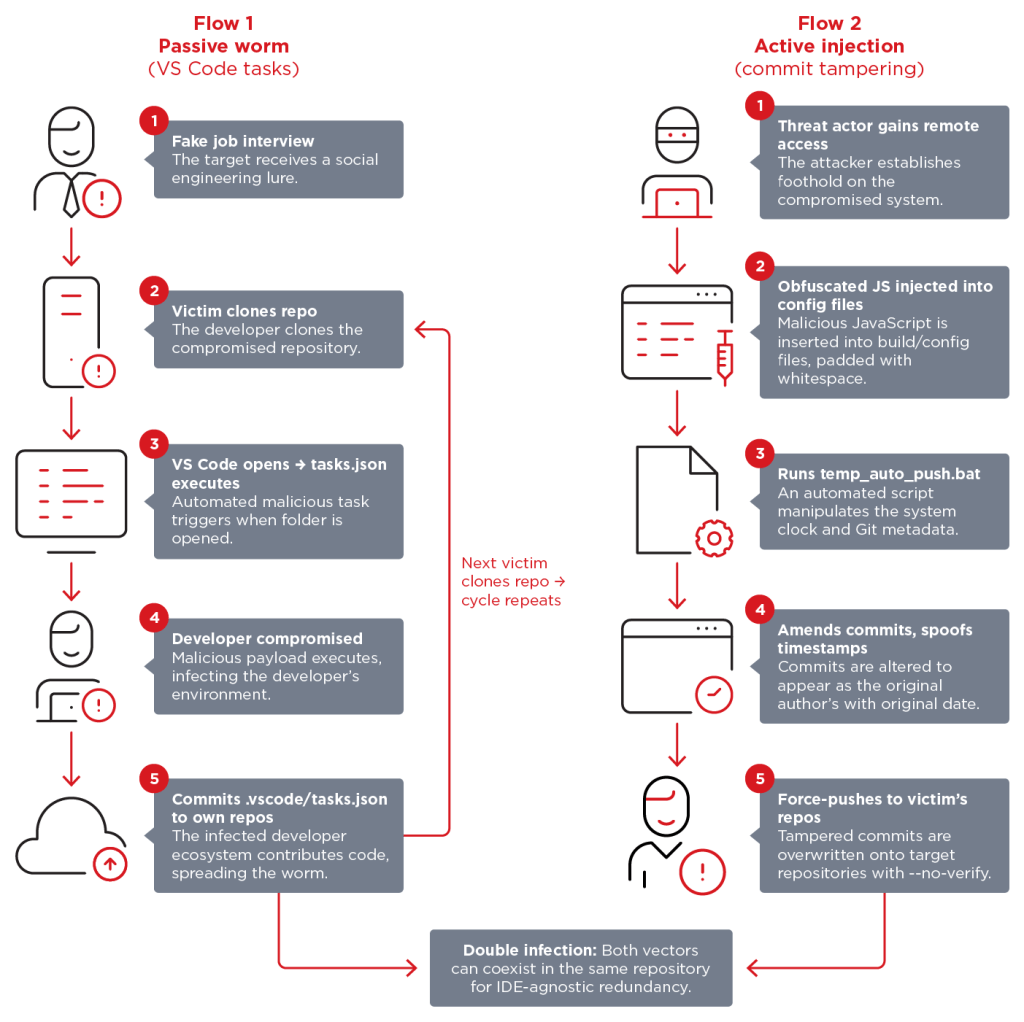
Analyst Comment: The campaign shows how effective it is to target devs directly through the tools and workflows they already trust. Void Dokkaebi positions themselves to be invited in through normal hiring and collaboration processes. Once code execution happens, the rest of the intrusion looks like a standard post-compromise flow.
There’s also a scaling factor here where compromised repos and packages can extend access well beyond the initial target, especially in environments where code is reused or integrated quickly. That turns a single successful lure into broader supply chain exposure.
This mirrors parallel activity from BlueNoroff described above, which is targeting the same sector through direct social engineering and identity-based access. Taken together, these campaigns show DPRK actors approaching the same problem from different angles: one focused on individuals, the other on the environments they build and operate in.

Leave a comment